Hashicorp
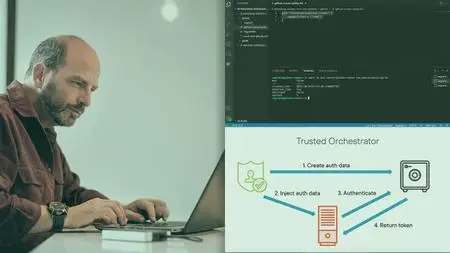
Integrating HashiCorp Vault in DevOps Workflows eBooks & eLearning
Posted by IrGens at Nov. 29, 2021
Integrating HashiCorp Vault in DevOps Workflows
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 54m | 242 MB
Instructor: Chris Green
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 54m | 242 MB
Instructor: Chris Green
HashiCorp Vault Enterprise 1.15.5 Software
Posted by melt_ at Feb. 2, 2024
HashiCorp Vault Enterprise 1.15.5 | 268 Mb
Manage secrets and protect sensitive data. Create and secure access to tokens, passwords, certificates, and encryption keys.
HashiCorp Consul Enterprise 1.17.2 Software
Posted by melt_ at Feb. 2, 2024
HashiCorp Consul Enterprise 1.17.2 | 135.1 Mb
Automate service networking across clouds. Discover and securely connect any service on any runtime.
HashiCorp Nomad Enterprise 1.7.3 (x64) Software
Posted by melt_ at Feb. 2, 2024
HashiCorp Nomad Enterprise 1.7.3 (x64) | 51.6 Mb
Deploy and manage any app on any cloud. Orchestrate containers, legacy workloads, and batch jobs.
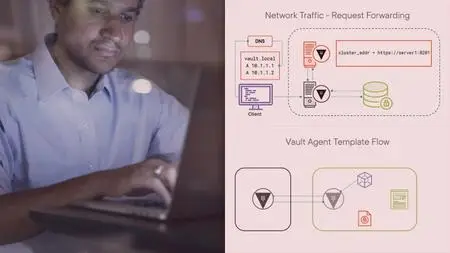
HashiCorp Certified Vault Associate: Vault Management eBooks & eLearning
Posted by IrGens at April 17, 2021
HashiCorp Certified Vault Associate: Vault Management
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 2h 47m | 338 MB
Instructor: Ned Bellavance
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 2h 47m | 338 MB
Instructor: Ned Bellavance
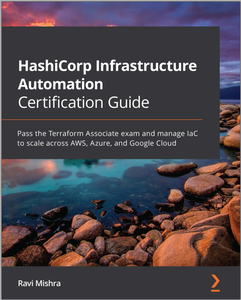
HashiCorp Infrastructure Automation Certification Guide eBooks & eLearning
Posted by yoyoloit at July 16, 2021
HashiCorp Infrastructure Automation Certification Guide
by Ravi Mishra
English | 2021 | ISBN: 1800565976 | 350 pages | True (PDF EPUB MOBI) | 52.5 MB
by Ravi Mishra
English | 2021 | ISBN: 1800565976 | 350 pages | True (PDF EPUB MOBI) | 52.5 MB
HashiCorp Boundary Enterprise 0.13.2 Software
Posted by melt_ at Aug. 26, 2023
HashiCorp Boundary Enterprise 0.13.2 | 5 Mb
Simple and secure remote access. Access any system from anywhere based on user identity. Boundary provides access to applications and critical systems with fine-grained authorizations without managing credentials or exposing your network.
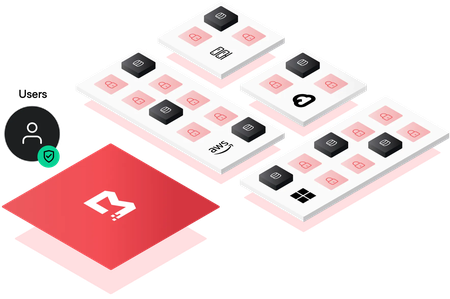
HashiCorp Boundary Enterprise 0.15.0 Software
Posted by melt_ at Feb. 2, 2024
HashiCorp Boundary Enterprise 0.15.0 | 251.1 Mb
Simple and secure remote access. Access any system from anywhere based on user identity. Boundary provides access to applications and critical systems with fine-grained authorizations without managing credentials or exposing your network.
HashiCorp Certified Terraform Associate eBooks & eLearning
Posted by IrGens at April 3, 2021
HashiCorp Certified Terraform Associate
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 2h 31m | 1.03 GB
Instructor: Moosa Khalid
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 2h 31m | 1.03 GB
Instructor: Moosa Khalid
HashiCorp Vault Enterprise 1.13.2 Software
Posted by melt_ at May 25, 2023
HashiCorp Vault Enterprise 1.13.2 | 101.3 Mb
Manage secrets and protect sensitive data. Create and secure access to tokens, passwords, certificates, and encryption keys.